Introduction
When people hear the word blockchain, the first thing that often comes to mind is Bitcoin or cryptocurrency. While it’s true that blockchain technology powers cryptocurrencies, the two terms are not interchangeable. In fact, the widespread association of blockchain with crypto has caused significant confusion and even skepticism in the general public.
This blog post aims to clear up that confusion. We’ll explain the fundamental difference between blockchain and cryptocurrency, and explore the wide array of real-world applications of blockchain technology — far beyond digital currencies.
What Is Blockchain?
At its core, blockchain is a type of distributed ledger technology (DLT). Think of it as a secure, digital record-keeping system that is shared across a network of computers. Each record (or “block”) is linked to the previous one, forming a “chain” that is immutable — meaning it cannot be altered once added.
The key features of blockchain include:
- Transparency: Everyone in the network can view the same data.
- Security: Data is encrypted and validated through consensus mechanisms.
- Decentralization: No single authority controls the network.
- Immutability: Records are permanent and tamper-proof.
What Is Cryptocurrency?
Cryptocurrency is a digital or virtual currency that uses cryptography for security. Cryptocurrencies like Bitcoin, Ethereum, and many others use blockchain to record transactions securely and transparently.
In simple terms:
Cryptocurrency is just one application of blockchain technology — not the technology itself.
Why the Confusion?
The confusion arises because Bitcoin was the first popular application of blockchain technology. For many people, their first and only exposure to blockchain has been through crypto trading, investing, or news coverage related to scams, price swings, or regulatory crackdowns.
This limited exposure creates the false impression that blockchain equals cryptocurrency, which is far from the truth.
Blockchain Applications Beyond Cryptocurrency
Here are several industries where blockchain is being used today — without involving cryptocurrencies:
1. Supply Chain Management
Blockchain allows companies to track goods from their origin to the end consumer. This improves transparency, prevents fraud, and ensures ethical sourcing (e.g., tracing whether diamonds or cocoa are conflict-free).
Example: IBM’s Food Trust platform helps companies trace the journey of food items, improving safety and reducing waste.
2. Healthcare
Blockchain can be used to secure patient records, ensuring that data is accessible only to authorized parties and protected from tampering or hacking.
Example: MedicalChain and other projects use blockchain to allow patients to control access to their own health data.
3. Voting Systems
Blockchain can power secure, transparent, and tamper-proof digital voting, potentially solving problems of election fraud and increasing voter trust.
Example: Estonia and some U.S. states have piloted blockchain voting systems.
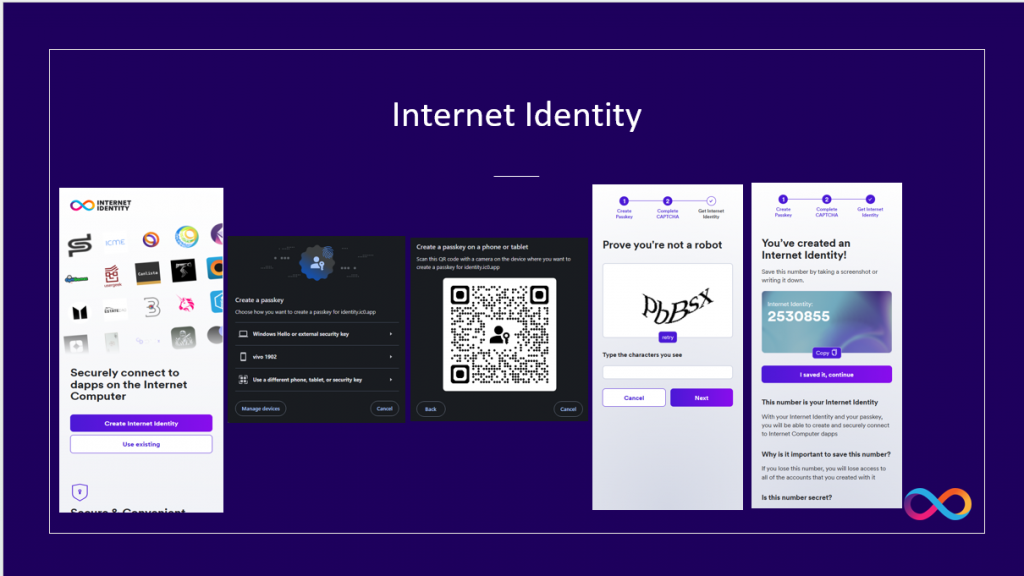
4. Digital Identity
Blockchain can be used to create self-sovereign digital identities that are secure and verifiable — reducing identity theft and simplifying access to services.
Example: Projects like ID2020 and Sovrin aim to provide blockchain-based digital identity systems for refugees and underserved populations.
5. Finance and Banking (Beyond Crypto)
Banks are using blockchain for cross-border payments, smart contracts, and real-time settlement — increasing speed, reducing fees, and improving security.
Example: JP Morgan’s Onyx platform and RippleNet use blockchain for fast, international transactions without relying on cryptocurrencies directly.
6. Real Estate and Land Registry
Blockchain can simplify the process of buying and selling property by recording ownership, preventing fraud, and reducing paperwork.
Example: Countries like Sweden and Georgia have adopted blockchain to record land titles.
7. Education and Credentials
Universities and institutions are issuing tamper-proof academic certificates on the blockchain that are instantly verifiable by employers.
Example: MIT issues blockchain-based diplomas that graduates can share with employers or institutions globally.
Final Thoughts
It’s time to separate the technology (blockchain) from just one of its use cases (cryptocurrency). While cryptocurrencies have their place, the potential of blockchain stretches far beyond digital coins.
From revolutionizing healthcare and education to transforming government and finance, blockchain is poised to be one of the most impactful technologies of our time.
Understanding this distinction helps us better embrace innovation — and move past the hype or fear often associated with crypto headlines.
Call to Action
If you’ve only associated blockchain with Bitcoin, now is the time to dig deeper. Explore how this powerful technology can transform industries and improve trust, transparency, and efficiency in everyday life.
Stay informed. Stay curious. The future is blockchained — with or without the coins.